by Paul Curzon, Queen Mary University of London
Reality is weird, very weird. The first thing you have to do to understand the reality of reality is to drop your common sense. Only then can you start to understand it especially when it comes to the quantum world of the very small. Our brains evolved to naturally make sense of human scale things, rather than the very large or very small. Accept the weirdness, though, and there are lots of opportunities, especially for computer scientists. That is why it is now an exciting area of research with theoretical physicists, engineers and computer scientists working together to make progress.
Not common sense
Imagine you are a person trying to understand the world a thousand years ago. Clearly the world MUST be flat. It looks flat and suggesting you are standing on a sphere is just ridiculous. People living on the other side would obviously fall off if it was a sphere! Except the world is a sphere and people in Australia (or Europe if you are Australian) don’t fall off. Common sense doesn’t work (until you understand how gravity works). That’s why science is so powerful. Common Sense also doesn’t work for understanding the reality of the very small. This branch of physics, quantum physics, is very important for computer scientists not only because the building blocks of our computers are becoming ever smaller, but because when you get so small that the laws of quantum physics matter, computers can work in new, exciting ways, ways that are far better than our current computers.
Bits and qubits
Let’s start with binary, the fundamental way we represent information in a computer. The basic building block of information is the bit. A bit is something that can have one of two states. It can be a 1 or a 0. That means a bit can store some information. These two states of 1 and 0 might be physically represented in lots of ways, such as a high voltage stored versus a low voltage stored, or a pulse of light versus no pulse of light, or someone’s hand up versus their hand down. If you have two bits then you can store one of 4 pieces of information in them because of the possible combinations (00, 01, 10 and 11), with three bits and you can store 8 different things. Those collections of bits can then stand for different numbers (that is all binary is), and by building big circuits from simple basic circuits that do simple manipulations on bits (i.e., logic gates) we can do ever more complex calculations with them and ultimately everything our current computers are capable of.
The spin of an electron
Bits can be represented by anything that has 2 states. So suppose you want to represent your bits using something really small like electrons. Electrons have a property called spin. You can imaging them as spinning balls of charge (though they are not exactly spinning like a spinning ball … electrons aren’t balls and they aren’t actually rotating in the normal sense – remember reality is weird so these analogies are just there to help give an idea, but it is never as simple as that). Now, electrons can “spin” in exactly one of two ways called spin up and spin down. There are only two possible kinds of spin because in the quantum world things come in discrete amounts, not continuous ones. They jump from one state to another, like a pedestrian (walk/don’t walk) traffic light going from red to green instantly) rather than gradually changing between them (such as the way a car gradually speeds up to the speed limit). An electron is either spin up or spin down, like the pedestrian lights, never something in between.
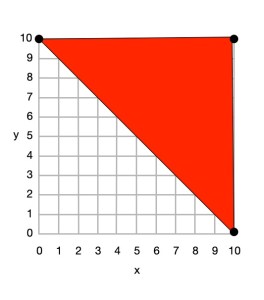
Now, it is possible to set the spin of an electron and to measure whether it has spin that is spin up or spin down, so an electron can, in principle, be used to store a binary bit given it has two states (spin up for 1 and spin down for 0, say). However, this is where weirdness really comes in. It turns out that it is possible for an electron to be both spin up and spin down at once as long as the spin is not measured, due to the way the quantum world works. A quantum pedestrian light doing a similar thing would have only one light that could be red or green. However, it would be both red and green at the same time UNTIL someone looked at it to see which state it was in (so measured the state). At that point they would become, and the person would only see, one colour or the other. This is called quantum superposition. To understand this it is better to think about reality being about probabilities not certainties. Imagine that the electron is like a tossed coin that is still in the air. It has a probability of being Heads and of being Tails. Only when it lands (so is measured) is it actually one or the other. An electron is combining both possibilities until the spin is measured.
The quantum tortoise and the hare
You may have the quaint idea that reality is made of sub-atomic particles (like electrons or protons) that are solid little bits of matter that are very ball like and exist in one place at any given time. Actually they aren’t like that at all. It is better to think of particles as just having probabilities of being at one place or another – they are kind of smeared across space, everywhere at once, like a ripple pattern across a pond, just with different probabilities of actually being in any place when their position is measured. When you do measure their position you find they definitely are in one place or another, appearing to be a particle again, not a wave.
It may help to think of this in terms of watching slow moving tortoises and fast moving hares passing you as they race. The position of a slow moving tortoise you see wander by is easy to call: it has a very high probability to be in a particular place. The position of a fast moving hare that whizzes past is much harder to call: it has a far lower probability to be in a given place at any time. However, without looking you can’t tell. You just know the probabilities. Of course with particles it isn’t exactly like that just as an electron’s spin isn’t exactly like a ball spinning. It is only when a particle’s position is actually checked (i.e. measured) that it is definitely at a known place and that smeared probability collapses to certainty. A quantum tortoise and hare racing past would be in all possible positions round the race track just with different probabilities. Suppose you only checked (so measured their position) at the finish line. It is only because of that measurement that the probabilities of where they were through the race turn into specific measured so known positions with a quantum hare or a quantum tortoise having actually won.
This weirdness is linked to the fact that the fundamental components that reality is made up of are both particles in given places (think of an electron or a proton) and waves passing through space (think of light or ripples in a pond) at the same time. So light behaves like a particle and like a wave. Similarly, an electron does too.
Electron spin as Qubits
Other properties of sub-atomic particles act in the same way as a particle’s position being smeared across lots of possibilities at once. This includes the spin of an electron. Until it is measured, an electron is superposed in both a spin up and spin down state at the same time (spinning both ways at once!): there is just a probability that the electron is in each state, it isn’t actually definitely in either. That means as long as you do not measure its spin, the electron as a device storing a piece of information is storing both 1 and 0 at the same time, each with a given probability. As such it behaves differently to an actual bit which must be either 1 or 0. We therefore call such an electron-based storage a qubit rather than a bit.
In theory, we can do computations on qubits manipulating and combining them in simple ways using the quantum equivalent of logic gates. Once we have created quantum logic gates to do simple manipulations, we can combine those gates into bigger and bigger circuits that do more complicated quantum calculations. As long as the states of the qubits are not measured all the states through the circuit are superposed in both states with particular probabilities. Unlike a normal circuit which does one series of computations based on its inputs, these quantum circuits are in effect doing all possible computations of that circuit at once. It is only when we measure the answer at the output, say, that the qubits in the circuit are fixed at either 1 or 0 and an actual result is delivered. This is like the tortoise and hare being everywhere (whatever racing strategy they followed) with some probability until we measure the result at the finish line (the output of the race). Because all states existed at once, lots of computation exists simultaneously, this means that such a circuit can, in theory, and with the right algorithms, deliver answers far, far faster than a conventional circuit could possibly do, given the latter can only do one computation at a time,
From theory to practice
That is the theory, and it is gradually being realised in practice. Qubits can be created and their values changed. Various quantum logic gates have also now been invented and so small quantum computers do now exist. Quantum algorithms to do certain tasks quickly have been invented. Since the original ideas were mooted, progress has been relatively slow, but now that the ideas have been shown to work in practice, more and more is being achieved, making it an exciting time to be doing quantum computing research.
More on …
- Quantum Computing (to come)
Subscribe to be notified whenever we publish a new post to the CS4FN blog.
This blog is funded through EPSRC grant EP/W033615/1.